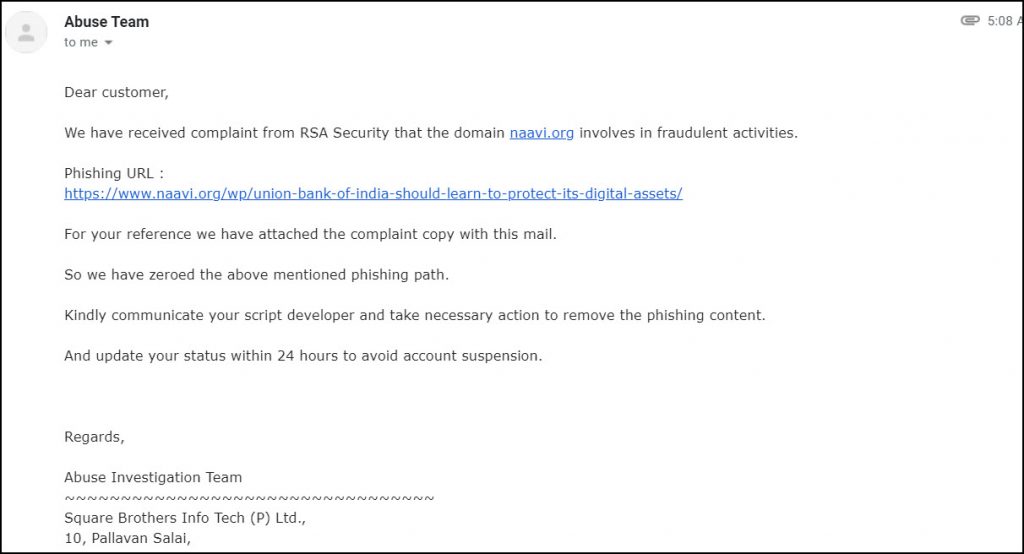
Today, I woke up in the morning to see the following email from my hosting service provider
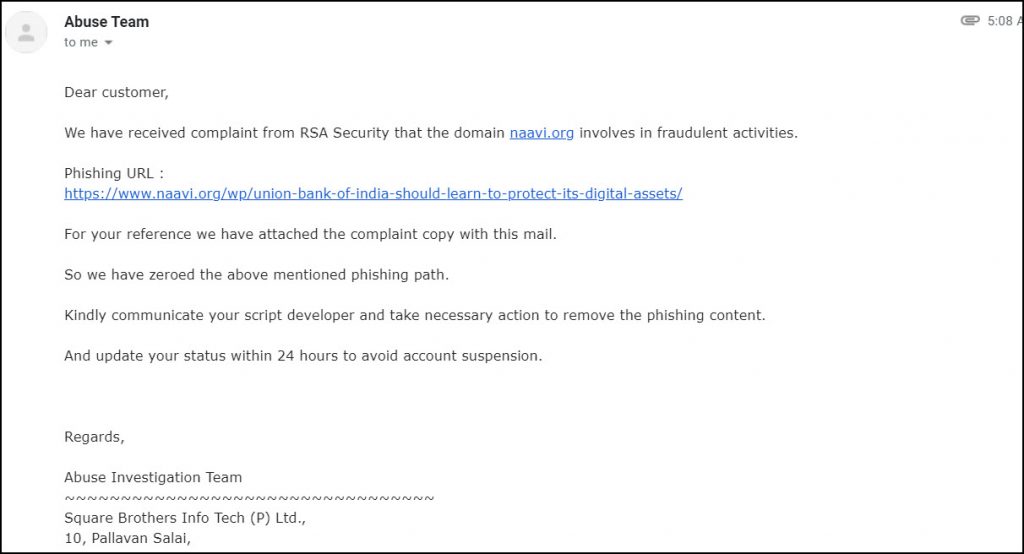
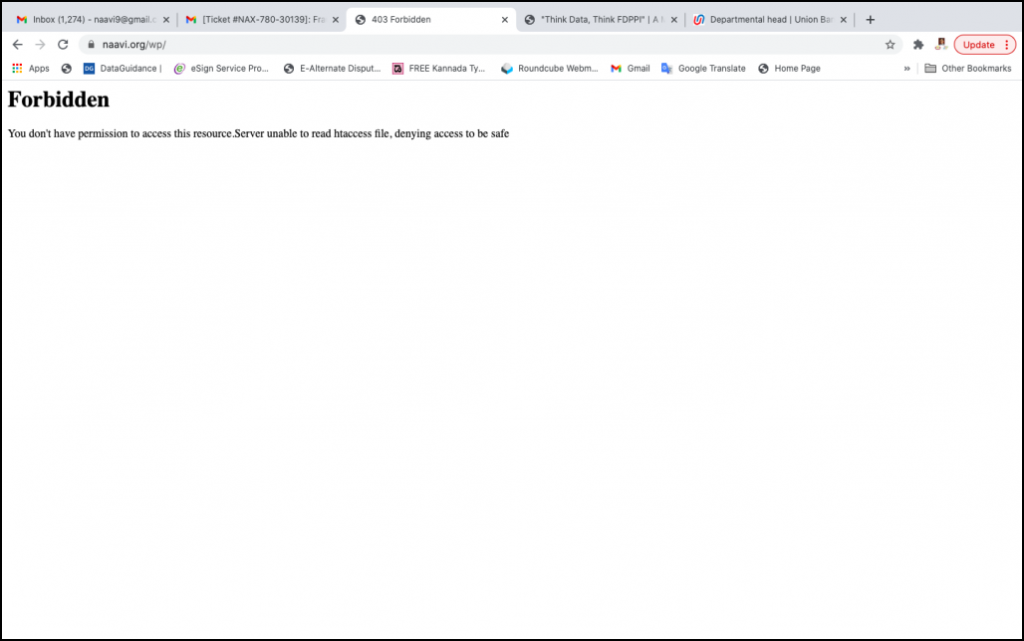
The Email suggested that a Phishing Script has been hosted at www.naavi.org in its article on Union bank published on January 14, 2021 (second article) and a complaint had been received from RSA security. The service provider had disabled not only the article page but the entire website www.naavi.org.
Old followers of Naavi.org are aware that long time back, one of the articles of Naavi published on a blog site (www.bloggernews.net) had been blocked which attracted a wide discussion on “Censorship” by the Government. That was in connection with an article on Zone-H.org website on which some comments had been made by the owner of Zone-H.org which was found unpalatable to a company in Hyderabad and the MeitY had blocked the article and the entire blog site as a mistaken implementation of the “Contempt of Delhi High Court order”. It indicated that MeitY (It was DIT at that time) had not applied its mind in issuing the blocking order. Subsequently the blockade was removed. Even before this, Naavi had also taken up another case when Meity had blocked the entire Yahoo Groups for blocking one group in Manipur.
Now a similar incident had arisen in the morning with RSA sending a notice to my service provider Squarebrothers.com which is a Chennai based hosting and internet service provider with whom I am having a nearly 25 year relationship.
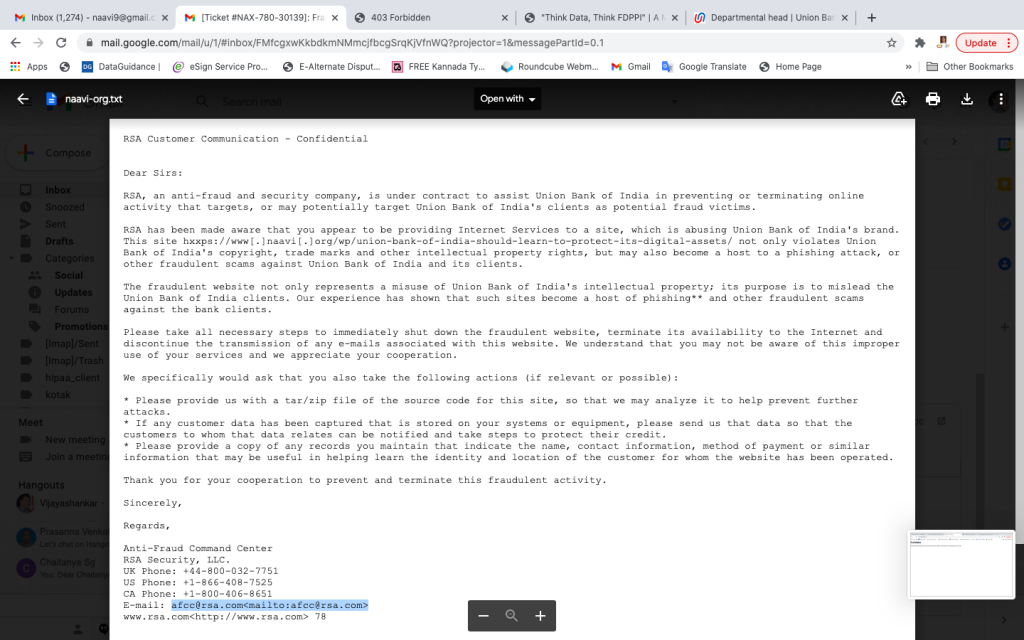
The RSA notice copy of which is given below made some accusations which need to be re-iterated.
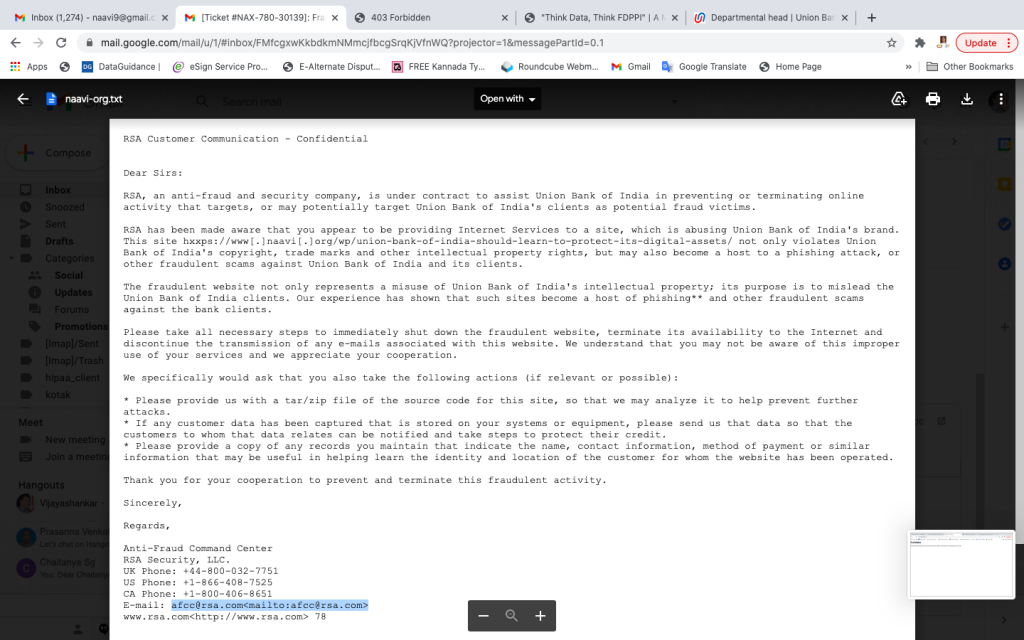
RSA in its message sent to Square Brothers, stated
“RSA has been made aware that you appear to be providing Internet Services to a site, which is abusing Union Bank of India’s brand. This site hxxps://www[.]naavi[.]org/wp/union-bank-of-india-should-learn-to-protect-its-digital-assets/ not only violates Union Bank of India’s copyright, trade marks and other intellectual property rights, but may also become a host to a phishing attack, or other fraudulent scams against Union Bank of India and its clients.”
It went ahead and branded naavi.org as a fraudulent website stating
“The fraudulent website not only represents a misuse of Union Bank of India’s intellectual property; its purpose is to mislead the Union Bank of India clients. Our experience has shown that such sites become a host of phishing** and other fraudulent scams against the bank clients.”
RSA then directed Square brothers
“Please take all necessary steps to immediately shut down the fraudulent website, terminate its availability to the Internet and discontinue the transmission of any e-mails associated with this website. We understand that you may not be aware of this improper use of your services and we appreciate your cooperation.”
I would like to state that the RSA Security team which has drafted this message must be some kids who donot know that Naavi.org is a website which has for over 22 years has been providing services for fighting Cyber Crimes and Phishing.
The message started with the words
“RSA, an anti-fraud and security company, is under contract to assist Union Bank of India in preventing or terminating online activity that targets, or may potentially target Union Bank of India’s clients as potential fraud victims.”
The trigger for this development was the article in which I pointed out that Union Bank which took over Corporation Bank and Andhra Bank had abandoned the earlier domain names of the two Banks. By doing so, and deciding not to invest Rs 800/- per year per domain to protect the digital asset, they would be losing the traffic to the website which would continue for a long time. This is the valuation aspect I have discussed in detail in the said article.
More than this exploitation of the traffic, I was concerned that the domain names would soon be registered by fraudsters who would be committing phishing frauds on the erstwhile customers of these two Banks.
My intention was to warn Union Bank that any such phishing would result in a liability on Union Bank. I was also highlighting the need for valuation of digital assets and bringing it into the books of account.
It is unfortunate that Union Bank nor the RSA team has read the article and understood what the article contained. Instead , RSA jumped to the conclusion that Naavi.org itself was a phishing site. By doing so, they exhibited their utter inefficiency to protect the Union Bank interests. Instead of shooting the thief, they were shooting at the guard.
By their action, RSA caused “Denial of Access” as for as Naavi.org was concerned, which is an offence under Section 66 of ITA 2000.
According to ITA 2000, Section 69, Government has the powers of blocking websites for which there is a process and the authority remains with the Home Secretary. Any other person blocking a website would be an unauthorised act which is punishable under Section 66 of ITA 2000. Civil liabilities can also be claimed under Section 43 of the Act. The Supreme Court judgement in the shreya Singhal case has also reiterated that intermediaries under Section 79(3) can only delete content on the basis of a Court order.
However, RSA arrogated to itself a judicial verdict that naavi.org was a “Fraudulent website” which is a defamatory statement. This was contrary to the Supreme Court verdict in the Shreya Singhal case.
Unfortunately, the service provider, in this case M/S Square brothers acted on the illegal notice from RSA and took down the website.
( Immediately after I pointed out to them the mistake, Square brothers not only re-instated the site, but also called me up to apologize).
In such cases it is necessary for service providers to raise a ticket, call for the views of the accused and take a decision. Naavi.org has given an earlier suggestion on how to handle “Rogue Websites” which could be adopted into the Incident Management System and the Grievance Handling mechanism of intermediaries.
I presume that after I wrote the article on Union Bank, it would have rightly attracted the attention of the CISO at Union Bank of India who would have, again not understanding fully what I wanted Union Bank to do in the instance, forwarded a mail to the RSA Security team saying perhaps…. “Please respond”.
The idiotic kneejerk response from RSA was to declare that Naavi.org was a fraudulent site, hosting a Phishing script and asking Square Brothers to block the site and also directing them
” We specifically would ask that you also take the following actions (if relevant or possible):
* Please provide us with a tar/zip file of the source code for this site, so that we may analyze it to help prevent further attacks.
* If any customer data has been captured that is stored on your systems or equipment, please send us that data so that the customers to whom that data relates can be notified and take steps to protect their credit.
* Please provide a copy of any records you maintain that indicate the name, contact information, method of payment or similar information that may be useful in helping learn the identity and location of the customer for whom the website has been operated.
Thank you for your cooperation to prevent and terminate this fraudulent activity.”
The RSA Communication was signed by Anti-Fraud Command Center
RSA Security, LLC.
UK Phone: +44-800-032-7751
US Phone: +1-866-408-7525
CA Phone: +1-800-406-8651
E-mail: afcc@rsa.com<mailto:afcc@rsa.com>
www.rsa.com<http://www.rsa.com>
The footnote to the RSA letter stated
“**”Phishing” is an e-mail scam that attempts to trick consumers into revealing personal information-such as their credit or debit account numbers, checking account information, Social Security numbers, or banking account passwords-through fake Web sites or in a reply e-mail. As described in the letter above, the fake web-site through which the fraudster is attempting to collect Union Bank of India’s customer data is under your responsibility.”
I wanted RSA to let me know where is the “Fake Website”, Where is the “Phishing Script” in Naavi.org and how Naavi.org becomes a “Fraudulent Website”.
On the other hand, I can call RSA as a fake Security services provider who cannot be trusted by the Bank. By their current action, they exposed both Union bank and Square brothers to legal action for defamation and the violation of several sections of ITA 2000. Having a security agency which does not know its legal obligations is a risk for Union Bank and I request Union Bank to revise its contract.
In case RSA has identified this, as a “Phishing Incident”, I want to know if they have notified CERT-IN and RBI about the potential security breach. If not, is it not another failure of their security service?
I also request RBI to examine this incident and advise banks not to appoint blind and un informed security agencies even if they carry the tag of “RSA” if the persons managing the “Command Center” donot know the difference between “Phishing” and “Reporting a Phishing possibility”. Most of RSA work is what they may call “Ethical Hacking” while we can call as “Potential Black hat hacking”. Such an agency passing its views on Naavi.org is like devil calling an angel as a fake.
I sent out a detailed e-mail to all the concerned persons today morning , immediately after which I got the response from Square brothers. But neither RSA nor Union Bank has come out with an apology for their unwarranted reactions and comments.
I look forward to them realizing that when they receive such complaints, they cannot let their robos take “Automated decisions” and launch an attack on a genuine website.
There has to be a human intervention to check if the robotic response was correct. Surrendering to Artificial intelligence and responses is idiotic to put it mildly. Indian law under Section 11 of ITA 2000 attributes such responses to the owners and they can be held liable.
If Section 85 is applied, the head of RSA and the Chairman of Union Bank as well as several other officials in the Bank and RSA are liable to be prosecuted for this action.
I hope that Union Bank realizes the extent of risk that they have pushed them into by the injudicious action by their security advisors namely RSA.
Comments are welcome
Naavi
Reference: E Mail sent to various parties in UNion Bank, RSA, SquareBrothers, Meity
P.S: End of the day, Union bank called to express regrets. Hopefully the Bank will enquire how did RSA was prompted to issue a “Take down order” without verification of the content and expose the Bank and its executives to criminal liability. The Bank has to put in place a system of handling complaints. Bank can review the contract with RSA to incorporate a penalty clause to ensure that RSA is responsible for such actions. This is a case study to learn how a Techno Legal incident needs to be recognized and responded. RSA needs to review its service if it has to remain credible as a security provider for Banks.
I thank a number of my friends who responded with suggestions during this incident. One of them pointed out that RSA has been using a similar notice for such incidents since last 10 years by sending me a copy of one such notice. This indicates that RSA is really not aware of its legal position and whether it requires to make changes to its system. I am waiting for RSA to respond. Otherwise a complaint may have to be filed against RSA some time today.
Naavi
18.01.2021