[In continuation of the earlier article/s on PDPSI, we proceed to unravel the further details of the Personal Data Protection Standard of India (PDPSI). The objective of the standard is to make available a open source guideline to Indian Companies to comply with Privacy and Data Protection requirements that meet the standards of BS10012, GDPR as well as the Indian laws such as ITA 2000/8 and the proposed PDPA 2018.]
We have so far discussed some of the basic requirements of the PDPSI such as the need to have data classification, implementation responsibility, charter of implementation, measurability etc. We can now get to the second level of issues addressed by PDPSI which is the set of implementation controls.
The objective of PDPSI is to ensure the implementation of measures to meet the requirements of compliance. The measures could be technical, could be in the form of policies and procedures and could also be in the form of manpower training.
PDPSI recognizes the importance of people in implementing the Information Security. Hence “Motivating the work force” and “Measuring the motivational efforts of the organization” are considered part of the PDPSI.
While there could be many approaches to “Motivation” in the Information Security implementation, Naavi advocates the “Pentagon Model” of Information Security Motivation.
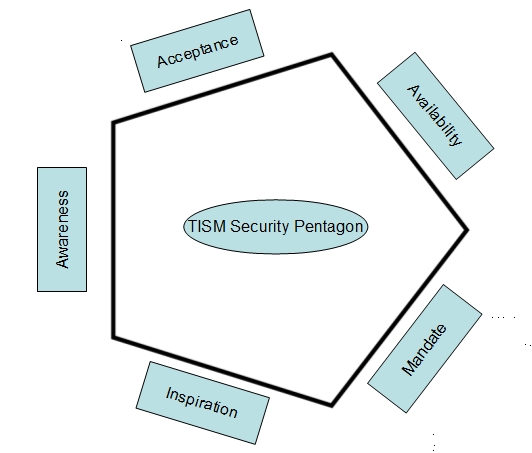
The “Pentagon Model” of the Theory of Information Security Motivation (TISM) suggests that there are five elements that need to work in tandem for proper implementation of Information Security in an organization. They should support each other and form a tight enclosure so that there is no leakage security.
The five elements consist of “Awareness” which is a training requirement, “Mandate” which is a “Policy” requirement and “Availability” which is “Technical Tool” requirement. In addition to these three, “Acceptance” and “Inspiration” are added as additional necessities to motivate people ” to accept what is imparted in the training”, “to respect and follow what policies are prescribed” and “to use the technical tools” that may be provided by the organization.
Conversion of “Awareness” to “Acceptance” is a completely behavior management issue to be handled by the HR experts in the organization. “Inspiration” is one aspect which is more an internal attitudinal factor of an individual and the organization can only try to trigger the inspirational instincts through innovative HR practices.
The PDPSI provides several controls mainly through policies to meet the requirements of TISM. The effect of such implementation needs to be captured by the auditor in the course of the audit.
Some of the measures of motivation can be captured in objective terms but most of them are subjective in nature. For example, we can measure whether 80% or 90% or 99% of employees have attended training programs and passed the relevant tests.
It may also be possible to conduct behavioural analysis tests to measure the level of acceptability of key elements of security behaviour through specially designed behaviour tests.
But measuring the “Inspirational” readiness of people may not be easily converted into objective parameters.
But there can be an identification of the efforts that the management has taken to inspire the work force to building an information security culture which can be recognized by the auditor and taken note of under the heading of “Commitment” indicated under the 5X5 DTS system.
(To Be continued)
Naavi
Earlier Articles
- A Step beyond BS10012 and GDPR-Personal Data Protection Standard of India-PDPSI
- Data Protection Standard of India- (DPSI)
- Data Classification is the first and most important element of PDPSI
- Why 16 types of Data are indicated in PDPSI?
- Implementation Responsibility under Personal Data Protection Standard of India
- India to be the hub of International Personal Data Processing…. objective of PDPSI
- Principles of PDPSI
- Naavi’s Data Trust Score model unleashed in the new year
- Naavi’s 5X5 Data Trust Score System…. Some clarifications
- Naavi’s Data Trust Score Audit System…allocation of weightages








