P.S: Yesterday, Supreme Court could not hear the DPDPA Constitutionality challenge from PIL lawyers due to other Constitutional cases being heard. A new Date will be known shortly and updated…It is now 364 days counting before DPDPA becomes fully operative.
Economic Times today carried an article titled “Battle Over India’s 1st Privacy Law Likely to Begin in SC by May End” under the by line “Suraksha P and Indu Bhan”.
 The article quoted Mr Hardeep Sachdeva, Senior Partner AZB & Partners and Arjit Benjamin Associate partner at Prosoll Law and Mr Rajas R Chitnis, Partner Chitnis Desai Law Firm.
The article quoted Mr Hardeep Sachdeva, Senior Partner AZB & Partners and Arjit Benjamin Associate partner at Prosoll Law and Mr Rajas R Chitnis, Partner Chitnis Desai Law Firm.
The law firms have been quoted as if they add credibility to the PILs which challenge the Act and ask for its scrapping. However, the lawyers have only stated that “Importance of the petitions cannot be understated. They collectively place India’s entire digital Governance architecture under Judicial scrutiny”. This is an example of “Journalistic Misuse”.
The article quotes an year old incident that on March 2026, 2025, 120 MPs from the I.N.D.I.A. block urged repeal of Section 44(3) of the Act because it undermined public interest. It also quoted the reply of Mr Ashwini Vaishnaw who had stated
“The DPDP Act, as outlined in Section 3, provides exemptions for personal data that is ‘made or caused to be made publicly available’ by individuals or entities under legal obligations. This ensures transparency while maintaining the need for privacy.”
The authors however missed or deliberately ignored that FDPPI in its intervention petition and Naavi through the many articles here has demolished the arguments presented by the Petitioners.
The article cites
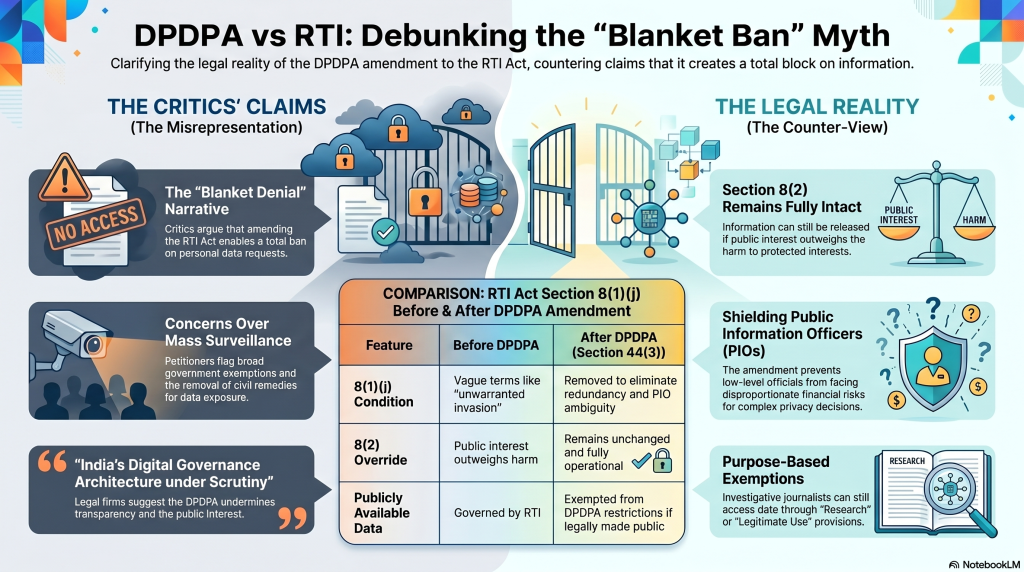
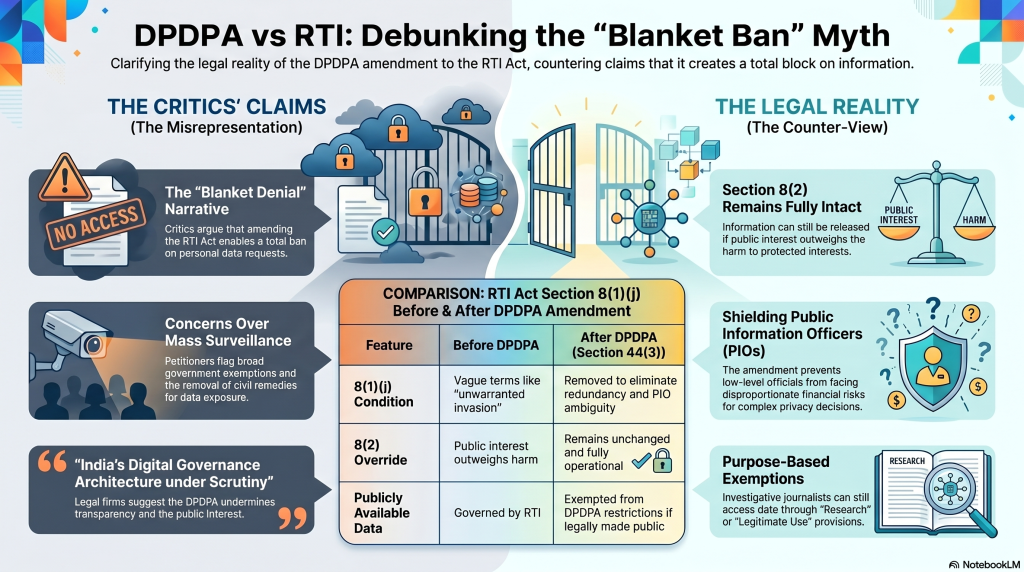
” Among other aspects, they (Ed:petitioners) have questioned provisions which amend the Right to Information (RTI) Act and allegedly enable blanket denial of information requests involving personal data.
Other challenges target broad government exemptions, concerns over mass surveillance and unrestricted state access to data. Some petitions also flag the removal of civil remedies for negligent data exposure.”
The article fails to mention the news item that the hearing which was scheduled to take place yesterday did not take place for whatever reason and it will be heard later.
If the authors wanted to summarize the PIL, then they could have also indicated that there is a Counter view that none of the objections raised by the petitioners are valid. Many of them arise out of misreading of the law and represent a biased view.
The authors fail to point out that
- The Supreme Court judgement of 2017 on Privacy which defined Privacy as a Fundamental Right altered the legal position in the country as was existing in 2005 when the disputed RTI section 8(1)(j) was constructed.
- The passage of DPDPA also exposed the PIO who violates privacy to a litigation from any affected individual.
- The current section 8(1)(j) does not provide any license to a PIO to release “Personal Information” in every RTI disclosure.
It states
“Notwithstanding anything contained in this Act, there shall be no obligation to give any citizen,information which relates to personal information.
-the disclosure of which has no relationship to any public activity or interest, or which would cause unwarranted invasion of the privacy of the individual unless the Central Public Information Officer or the State Public Information Officer or the appellate authority, as the case may be, is satisfied that the larger public interest justifies the disclosure of such information:
Provided that the information which cannot be denied to the Parliament or a State Legislature shall not be denied to any person.”
In the amendment proposed by Section 44(3) of the DPDPA, the condition starting with “-the disclosure…upto …any person” has been deleted.
At the same time RTI Act next paragraph under Section 8(2) states
“Notwithstanding a… any of the exemptions permissible in accordance with sub-section (1), a public authority may allow access to information, if public interest in disclosure outweighs the harm to the protected interests.”
What these two sub sections meant was that if “Public interest in disclosure outweighs the harm to the protected interests”, then there is no need to apply conditions mentioned in the section 8(1) and the information can be released. This section 8(2) remains even after the amendment through Section 44(3).
Hence the contention that the amendment proposed through Section 44(3) has in any way placed a blanket ban on release of information under RTI act and diluted it is false.
In the earlier version of the RTI act, there was a repetition of the exemption for “Public Interest outweighing the Privacy Rights” was duplicated under both 8(1)(j) and 892). It was redundant.
Further the use of words “Unwarranted invasion of Privacy”, “Larger public interest justifies disclosure” and “Outweighs harm to the protected interests” were vague expressions which were beyond the capability of a Government official in the position of a PIO to adjudicate. They are matters which require judicial expertise to adjudicate.
In the event the PIO is unable to decypher “What is the extent of harm” to some individuals “What is the extent of public interest”, “how one is greater or lesser than the other”, then his decision would be wrong and disclosure could pose a risk under DPDPA for the organization which is a data fiduciary.
If DPB imposes a fine on the organization and the head of the organization initiates disciplinary proceeding against PIO for not making the right decision, he would be exposed to a financial risk of a magnitude disproportionate with his responsibilities.
Hence it was untenable for imposing such an onerous responsibility on the PIO after DPDPA became effective. It was therefore mandatory for the Government to take the action as they have done.
Secondly if any RTI activist is not satisfied with the rejection of the information, he can always invoke the Court to intervene and interpret whether the need for release of the information outweighs the harm and even the PIO would be happy to abide by the order of the Court since it falls under the legitimate use of information under Section 7 of DPDPA 2023.
Beyond this, the clarification given by Ashwini Vaishnaw that information already made public is outside the provisions of the Act also needs to be noted.
In an RTI application the journalists argue that the release of personal information is required as a check against public corruption. Currently they can get the personal information of the official since it is part of the “Publicly made information” since the person is a Government official.
There cannot be a free license for the release of information of beneficiaries since even if there are a couple of cases of beneficiaries who are products of corruption, most others are in no way connected with the corruption and hence release of their information is a violation of their privacy. The Journalist who wants to expose corruption should be able to convince a Court of the need for release of the entire beneficiary list to expose if there are any undeserving beneficiaries.
Alternatively deidentified, or redacted information can be released which can be used for research without making the identity fully public.
In view of the above the objections raised by the petitioners on Section 44(3) is completely misplaced and has to be rejected.
We must also re-iterate that Journalists cannot be considered as a privileged community to whom DPDPA 2023 should provide an exempted access to the Private information of the individual citizens. DPDPA does not provide any such exemption for any profession like say Doctors, Lawyers etc. All exemptions are purpose based and DPDPA provides an exemption for “Research” which can be used by “Genuine Investigative Journalists”.
Hence the PILs filed in the Supreme Court by Mr Venkatesh Nayak, Geeta Seshu, Reporter’s Collective etc deserves to be rejected.
We request Journalists, Suraksha P and Indu Bhan to do better research before putting out an article of this nature.
Naavi