Here is another case of a hacker admitting publicly an offence for which he may get 3 to 7 years of imprisonment and challenging the Indian Government. The MeitY is not strong enough to either secure their systems nor prevent Indian software professionals trying to use the Government projects as target practice for testing their hacking skills.
In the bargain the Indian Government under Mr Modi appears to be powerless against people who are specifically targeting the Indian Government assets and exposing the other citizens to great risk.
I draw the attention to the article https://yetanothersec.com/blog/2020/06/03/digilocker-disclosure/
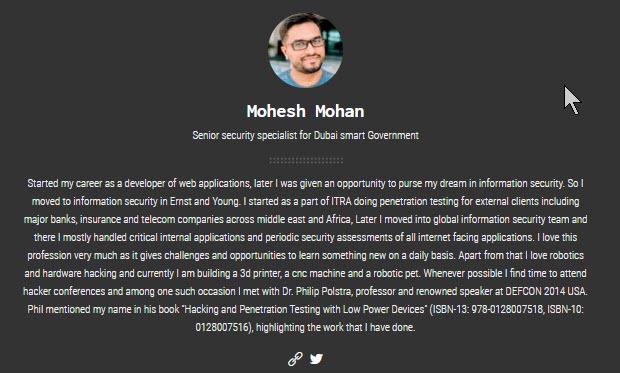
which has highlighted the exploits of Sri Mohesh Mohan, Senior Security Specialist for Dubai Smart Government.
I have no doubt that this person is a talented security specialist and his website (https://www.h4hacks.com/) may have proof of his talent. However, he represents that category of technology experts who are suffering from “Technology Intoxication” and focus their energies on hacking Government projects particularly of India because the Indian Government is meek in dealing with such persons.
In his article he admits that he was motivated by the “Competitive Hacking Urge” that he felt when the another software person from Bangalore announced that he has hacked the Aarogya Sethu app.
He has then targeted the digi locker app after downloading it . Rest of the article describes the modus operandi of the hacking just like how a psychopath describes how he murdered a person.
The fact that this person is proud of his act makes me wonder about the ethics of professionals.
I want to question the Dubai Government if it has assisted this person to hack the Indian Government assets by providing him any hardware, software, wifi connectivity etc., if so whether they would take the responsibility for the hacking.
It is clear that because the Aarogyasethu authorities handled the earlier hack with kid gloves, it has encouraged this hacking. Hence we should hold the officials who did not take stringent action on the AarogyaSetu hacker for encouraging Mr Mohesh Mohan for complicity in this fraud.
I am a DigiLocker holder and this hack has directly compromised my security for which I am entitled to claim damages from the Government of Indaia.
I seek an answer from the person in charge of the Digi Locker project, National e-Governance Division, MeitY on what action they intend taking against this hacker.
Has the Meity got Digilocker notified as a “Protected System” under Section 70 of ITA 2000?
Has the terms and conditions of use of Digilocker prohibit the downloading for reverse engineering and hacking purpose?
Is there a privacy policy and terms of use before the citizen first provides his Aadhaar number to the Digilocker authorities when some body downloads the app?
I would like to know from the Secretary of MeitY who will be held responsible for exposing mine and several lakh fellow Indian’s confidential information to the hacker who may sell it in the darkweb?
The reply from CERT-IN that the vulnerability has been plugged confirms that the vulnerability did exist and is a damning evidence against the Digilocker authorities.
The reply of the digilocker team is funny as it says “No account other than that of the attacker was used”. It does not say that the information of the 3 billion documents were not accessed by the hacker. The reply also says that the data is “Safe and Secure”. It is difficult to understand how compromised data is considered “Safe”.
The digilocker team does not perhaps understand that keeping data safe and not the data owner’s safe is not acceptable Techno Legal security.
The incident calls for a severe disciplinary action against the digilocker team along with initiation of criminal action against the hacker.
I am forwarding this article to the concerned persons and await their reply.
I hope MHA also takes necessary action since this incident is a crime which causes a serious concern for Indian citizens if their critical personal information such as the Aadhaar data, PAN data, Driving license data etc are safe.
Naavi
P.S: I have sent the following e-mail to digital locker team:
To: support@digitallocker.gov.in
Dear Digitlocker team
I have also sent the following message to CERT-IN:
To: incident@cert-in.org.in
To