Personal Data is a key corporate asset in this time of Data Driven Business. Organizations collect specific identifiable personal data some times in a structured manner through a form associated with a service request. This is an ideal situation when the entire set of data elements are collected in one shot along with a proper notice, purpose linkage, data minimisation etc.
But in actual practice an organization accumulates individual data elements often not specifically identifiable with a data principal. The “Personal Data identifiers” therefore become available but cannot be associated with any identifiable individual. Even when a “Name is available”, if it is concluded as belonging to a specific person which the Data Fiduciary knows, there could be a risk of mismatch. Hence an organization has to wait for accumulation of at least 2 parameters which together create an identity.
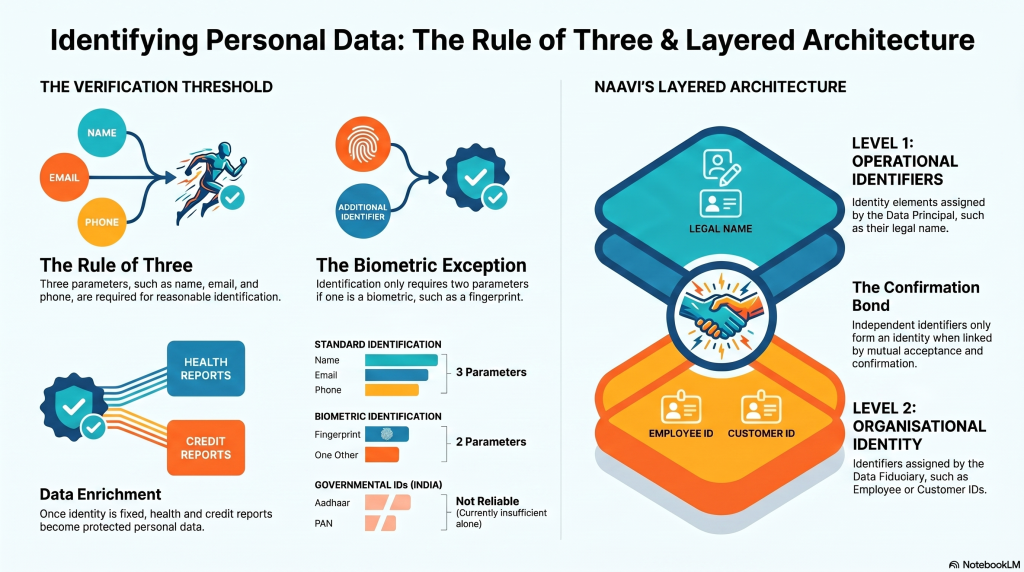
To be on the safer side it is better to have 3 parameters to identify a person unless one of the two parameters happens to be a “Biometric” information.
Under “Biometric” one can take the finger print, the facial photograph, the voice sample, DNA etc.
A Unique Government ID such as an aadhaar number or PAN number could perhaps have been considered equivalent to the biometric for identification but for the current state in India where these are not reliable.
In the absence of such “biometric ” data, there should be atleast 3 parameters such as the name, email and the phone to reasonably identify an individual.
Once the identity of an individual can be fixed with a reasonable certainty, information such as a “Behaviour Profile” or a “Health report”, “Credit Report” can be added to the personal information and will also form the data that needs to be protected under the Data Protection Law.
To capture this nature of Personal Data as a “Set of Data Parameters”, Naavi adopts the following layered approach to recognition of Personal data.
Level 1: Operational Identifier: Name (Assigned by the Data Principal)
Level 2: Organizational Identity: Employee ID, Customer ID (Assigned by the Data Fiduciary).
Level 1+Level 2 will have confirmation from the data principal and the data fiduciary provided the two are linked with acceptance from both. If the two identifiers are present independently they donot form an identity till they are associated with a bond of conformation. This could be through a request for confirmation sent from one of the two to the other and its acceptance by the other.
Level 3: Contact Layer: E Mail address, Mobile number
Level 4: Biometric layer: Finger Print, Facial Photograph, Voice Sample, Dental X ray, DNA etc.
Level 5: KYC layer: A KYC report generated by a trusted third party “Joint Data Fiduciary”
Level 6: Report level: Behaviour Profile, Health Report, Credit Report etc
We can organize these levels into a hierarchical system to move raw data as it flows into an organization into a “Provisional Personal Data Store”, process it periodically and move it to the next level
Naavi