WhatsApp has been in news as a messaging Company providing End to end encrypted messaging services in the past, introducing vanishing messages etc. As a messaging company it had its share of controversies involving spread of fake messages and mobilization people for creating social unrest etc.
Now by introducing the WhatsApp Pay, WhatsApp is changing its profile from a messaging app to a Fintech App. Perhaps we will need to look forward to a different set of issues arising between WhatsApp and the Government of India involving data localization and financial fraud control.
With RBI providing the regulatory clearance for WhatsApp Pay, users of WhatsApp can now send and receive money from their contacts just like exchanging messages. Additionally, payments can also be made to persons not in the contact list with the use of QR code.
WhatsApp is having a customer base of around 350 million in India and hence as a Peer to peer payment system it is expected to catch on quickly. Presently GooglePay and PhonePe are said to have a market share of around 40% each in the UPI based payment system worth Rs 3.5 lakh crore transactions per month, to which WhatsApp will join.
All these systems will use the UPI network of partner Banks and compete with the Wallet Companies and PPIs particularly for small payments, though they themselves donot undertake any liability for the transactions.
While GooglePay and WhatsPay are monetizing their customer base acquired from a different service, AmazonPay and PhonePe (taken over by Flipkart) may use the E Commerce customer base to spread their wings into the FinTech domain.
In terms of business strategy, the way messaging and e-commerce business is merging onto banking and finance business is interesting. The trend is “Unified Business Services” and these companies are enlarging their revenue base from advertising to financial services. Soon they will also wade into insurance and investment broking besides traditional banking itself.
Since these are “No Liability” monetization deals to encash on the customers they acquired when India did not have any Data Protection laws, they are great as business deals but uncomfortable for Fraud watchers.
Traditionally Banking has been separately regulated by RBI in India but the current developments indicate a trend where the frontal face of the business is a Google or WhatsApp or Amazon but the back end is the licensed banking service.
This creates a perception that WhatsApp or Google is the payment institution but actually the customers are authorizing these agencies to operate Customer’s Bank accounts as if they are power of attorney holders for operating the Bank account.
For example WhatsApp pay is having an arrangement with five banks namely the ICICI Bank, HDFC Bank, Axis Bank, SBI and Jio Payment Bank who are licensed to carry on banking business. When we use WhatsApp, we are allowing WhatsApp as our agent to operate our Bank account through a chain of third parties.
When a WhatsApp customer activates the payment system, he is assigned a unique WhatsApp UPI ID which includes the phone number. This is used as a QR code for receiving the payment and is therefore linked to the UPI Id of the customer in his preferred Bank account based on the mobile number.
While using the system, the payment link will immediately open the UPI app and the instruction is re-directed to the user’s Bank. User’s Bank sends the payment to the WhatsApp assigned UPI ID of the contact and at the destination this UPI ID has to be converted into the personal UPI ID of the contact through the intervention of WhatsApp.
The WhatsApp payment server (which could be different from the message server) therefore may be involved in converting the assigned UPI ID of the users to their real UPI Ids in their respective Banks and vice versa. The rest of the transaction is handled by the Banks.
The initiation of the service is therefore like an authority to operate the Bank account for a limited purpose. However the Customer may not realize that he is the Principal and WhatsApp is his agent for execution of the transaction. Since he inputs the PIN directly, we presume that it is not visible to WhatsApp. But WhatsApp is forcing the user to use the UPI app which he may not otherwise would like to use. It also holds several permissions and therefore it is not clear if the transaction data is visible to the WhatsApp server.
The “Request for Payment” prompts the issue of the payment instructions from the sender of the payment.
The authentication for the transaction is the 4 number PIN set by the customer for his UPI account with the Bank which is neither a digital signature nor a complex password. The only additional security that can be expected is the link to the mobile device and perhaps the SIM number. The mobile device therefore becomes critical to the security and if the device is lost, there is every possibility of the compromise of all the Bank balance one may have in multiple Banks to which the mobile has been registered.
By this convergence of messaging platforms with the Banks, the financial risks have multiplied. At the same time these UPI based systems have been designed in such a manner that the partner Banks of WhatsApp are acting as “Undisclosed Agents” of the front end messaging companies. Whenever there is a fraud, which is inevitable in a financial transaction, the consumer will therefore be searching for finding out who is responsible for the fraud.
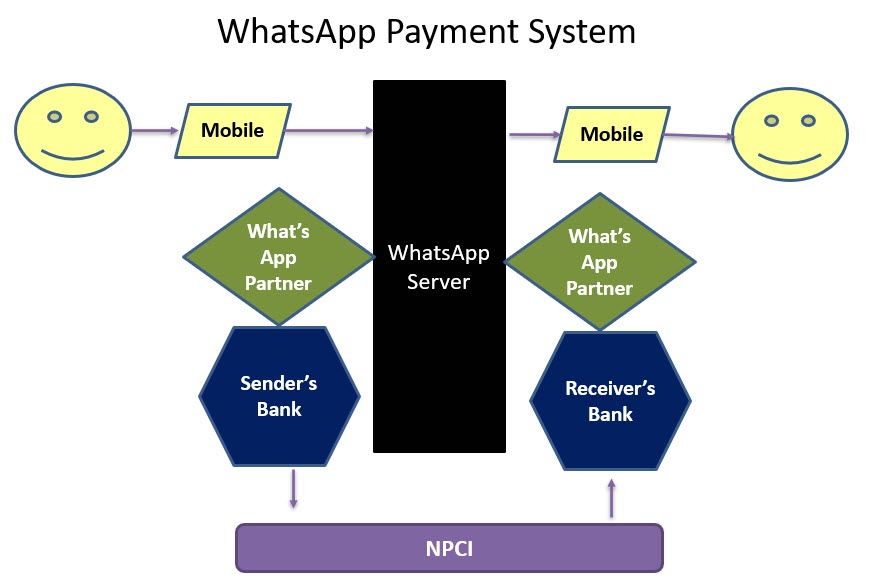
For example, in the WhatsApp Pay system there are 4 Banks involved in the back end (one each of the payer and the payee, one each of the WhatsApp accounts of the two parties who are partnering WhatsApp. Additionally NPCI is involved as the switch and WhatsApp as the front end at both the payer’s end and the receiver’s end. This is not disclosed in the Privacy Policy and no specific privacy policy is attached to this service.
The above diagram roughly suggests the institutional architecture of the WhatsApp pay system .
A fraudster can execute a fraud at any of these 8 points. A WhatsApp Spyware can compromise either of the two ends of WhatsApp, trojans can compromise the traditional banking channel and NPCI switch can be compromised by any other malware. The net result of manifestation of any of these vulnerabilities is that an unauthorized payment occurs and money is debited in the payer’s account.
RBI needs to confirm who will hold the liability for such frauds and whether the “Limited Liability” system applicable for other online frauds also applies for WhatsApp pay kinds of payments.
The Banker Customer relationship is between the Payer and his Bank and hence the liability for the unauthorized payment will first fall on the Paying Bank. This has to be clarified by the RBI.
Unfortunately the Bank would be in the background and the victim of a fraud would first try to contact WhatsApp to report a fraud. At present WhatsApp has not made any provision for reporting of disputes along with the payment message. (P.S: Google pay seems to have made such a provision).
Hence the victim may be required to run from pillar to post to lodge his complaint and get his money back. Every body will pass the buck and the victim would be told that he alone should be responsible for the fraud because every other organization has international level security while the user is ignorant, negligent and must have clicked a wrong button etc.
At present the liability for Banks for phishing frauds have been determined on the principles set by the S Umashankar Vs ICICI Bank case which has been decided at the Adjudicator’s level and confirmed at the TDSAT level, under ITA 2000. It has been held that under Section 43(g), non adherence to security measures mandated by RBI would amount to “Negligence” or “Lack of Due diligence” which legally becomes “Assistance to another for committing a fraud”. (See TDSAT Judgement here).
The principle established by this judgement places reliance on the RBI as a regulator to set the security standards. Additionally availability of any other guidelines under law would be applicable. Here the Section 43A of ITA 2000 and the reasonable security practice mentioned there in becomes relevant. The Due diligence mentioned under ITA 2000 extends now to the draft Personal Data Protection Bill 2019 which may soon become a law and substitute Section 43A.
Thus while settling the liability under the WhatsApp fraud, it would be relevant to invoke the provisions of ITA 2000 and PDPA of India under which WhatsApp would be a Data Fiduciary and all other agencies will be either Data Processors or Joint Data Fiduciaries.
At present WhatsApp does not have a Privacy Policy as required under PDPA nor ITA 2000. RBI has not been transparent about the details of the arrangement with WhatsApp apart from the total limitation of about 20 million users.
In particular we need clarification on whether RBI has exempted WhatsApp from the data localization principle or other due diligence requirements. We also need to know if RBI has flagged the risks to consumers and built any safeguards such as mandatory Cyber insurance.
In the meantime WhatsApp must make efforts to be compliant with PDPA on the basis of the current draft bill and upgrade it as and when the Act is finally passed.
It would be better for the Governor of RBI to come up with an assurance to the Country that the risks of allowing UPI based payment systems by the global giants has been properly assessed and adequately mitigated.
We therefore suggest that RBI should come up with a “Master Circular” to clarify the working how this system of payment systems operated by private non licensed Fintech players like Google, WhatsApp, Flipkart, Amazon etc., the Bank’s responsibilities and Customer’s rights.
Naavi









Your post was a very useful resource for me because of the abundance of information you provided on the subject. Finacus should be seriously considered by anyone looking for a cutting-edge banking solution with exceptional customer service.
Enterprise Solutions Services