Naavi.org was in the forefront of raising objection to the Section 43A rules of the MeitY in 2011 where the MeitY insisted that “ISO 27001 compliance” is deemed compliance of Section 43A.
When I first wrote “Is India selling itself out to ISO 27001?” or Has MIT issued the guidelines without proper evaluation? , “Is DIT misleading the Public”? etc., the Kapil Sibal led ministry was extremely unhappy because it was pointed out that if all Indian companies were made to undergo ISO27001, there would be a huge and useless burden on the industry.
Now that Section 43A is coming to the end of its lifetime and would be replaced by the Personal Data Protection Act, it is time to recall how Naavi’s concern that giving a prominence to ISO 27001 as “Deemed Compliance of Section 43A” was a blunder of the MeitY.
Dr Lal Pathlabs has given a perfect example to justify the point which I made in 2011 which the MeitY brushed aside.
Now going by the press reports, Dr Lal Pathlabs compromised millions of sensitive personal information of Indian public by storing them in Amazon cloud without a password.
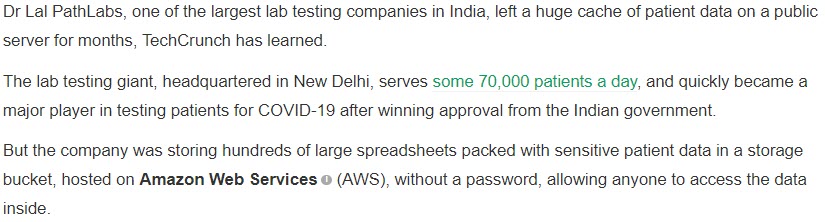
Techcrunch.com reports as under:
Quote:
Unquote:
Techcrunch also reports that the security loophole has since been closed, meaning that a password has now been set.
However what surprises me is that the website of Dr Lal Pathlabs does not show any information on the data breach. There is no information about CERT IN having asked for a report on the data breach as per powers available and duty cast on them under Section 70B of ITA 2000/8.
The “Privacy Policy” on the website covers only the information collected on the website and does not give clarity about the policies and practices related to the collection of information on their services.
The Privacy policy inter-alia suggests as follows:
Quote:
Information security
The Company has implemented appropriate security practices and standards and has a comprehensive documented information security programme and information security policies that contain managerial, technical, operational and physical security control measures that are commensurate with the information assets being protected with the nature of business. Further, the Company takes appropriate security measures to protect against unauthorized access to or unauthorized alteration, disclosure or destruction of data and restricts access to your personal data to the Company’s employees who need to have that information in order to fulfil your request or supply our services
Unquote:
This indicates that the privacy policy has been drafted in accordance with the words contained in Section 43A guidelines.
It is therefore not surprising to note that the company also sports ISO 27001 as one of its accreditations
It would be interesting to find out who gave the ISO 27001 accreditation to this company and with what scope and whether that would continue to be used even after the report of the current breach or would be withdrawn.
It is time for the industry to consider that ISO27001 is only a guidance tool and it cannot be considered as a stamp of everything being in order regarding the information security implementation in an organization.
I recall the reply I had received on 11th July 2011 from Mr Prafulla Kumar of DIT which stated as follows
However the notification contained the words
“A body corporate or a person on its behalf shall be considered to have complied with reasonable security practices and procedures, if they have implemented such security practices and standards and have a comprehensively documented information security programme and information security policies that contain managerial, technical, operational and physical security control measures that are commensurate with the information assets being protected with the nature of business.
In the event of an information security breach, the body corporate or a person on its behalf shall be required to demonstrate, as and when called upon to do so by the agency mandated under the law, that they have implemented security control measures as per their documented information security programme and information security policies.”
“The international Standard IS/ISO/IEC 27001 on “Information Technology – Security Techniques – Information Security Management System – Requirements” is one such standard referred to in sub-rule (1).”
In view of the above, despite the clarification provided to me directly, MeitY continued to give an impression to the public that ISO 27001 is a “Deemed Section 43A compliance”.
This false impression created by the MeitY is the reason why Dr Lal Pathlabs type of companies continue to ignore information security in its real sense and opt to buy the certification and remain complacent that every thing is fine with them.
I call upon the MeitY to clarify whether they are prepared to withdraw their endorsement of ISO 27001 at least now.
Making mistake once is understandable.
Standing on the ego and justifying it is undesirable.
But Not making amends and not apologizing for the mistake even after it is seen how an “ISO 27001 certified company can have sensitive data in Amazon storage without a password”, is unpardonable.
The data breach raises similar questions on other accreditation agencies like the CAP, NABL etc., who have to withdraw their certifications or at least conduct an enquiry and re-establish the credentials.
I also call upon the NSE and BSE to clarify whether Dr Lal Pathlabs filed any report with them that there was a data breach, there could be a PIL or Government penal action on the company and as a result there could be a financial risk to the share holders of the company.
We will continue to watch if the Clause 49 declaration applicable to listed companies will report the breach to the share holders in the annual report and whether the statutory auditors report the same in their audit reports.
(P.S: Deloitte Haskins & Sells LLP was the auditors of the Company some time back. After the ILFS fiasco, Deloitte could have faced some sanctions barring them from continuing their audit work. It appears that the matter is with NCLT).
There were 5 independent directors of the Company who also have many questions to answer along with the Company secretary.
I have also pointed out earlier that Adjudicating officers in multiple states can start an enquiry under Section 46 of ITA 2000 on the incident and PIL can be filed in any High Courts or the Supreme Court, provided the matter is considered as a serious privacy breach. Otherwise all the “I Love Puttaswamy Judgement” statements of privacy activists will only be considered as a TRP hogging drama.
Unless the regulatory authorities take such data breaches seriously and use it to define the future direction of compliance, such incidents will continue to happen in future.
Naavi