The WannaCry ransomware attack across 100+ countries attracted a huge attention of the media yesterday. It continues to be the main story in print media today. The developments on the ransomware has been fast and furious with security experts all over the world joining hands to find a remedy for Wannacry.
A few hours into yesterday, CERT IN joined in sending out its advisory but the advisory was a little too late to be of any practical help. But by that time most of the Anti Virus and anti malware companies had put out their advisories and it had been circulated by most security professionals and in discussions over social media including Naavi.org. Nevertheless this was one of the few occasions when CERT In did respond with an advisory within a short time and hopefully the trend will continue and improve in future.
One of the reasons stated for the delay is that CERT In has to wait for secondary confirmations before an advisory is sent. But there is no use in locking the stable after the horses had bolted. Keeping the nature of the organization which is CERT-In, I suggest that CERT-In should develop an “Incident Alert” which could go out as an “Intelligence Advisory” even when a security threat is not fully confirmed to the satisfaction of a Government Agency like CERT-IN and then follow it up with a full scale advisory. This will meet the needs of the market and preserve the conservative outlook on advisories to be held out by the Agency.
For the sake of records, we have given below some links which provide an excellent analysis of the Version 1 of the WannaCry ransomware.
This was “Accidentally” halted yesterday through an activation of the “Kill Switch” when a security professional analysing the malware code found that the encryption is activated only if the malware cannot connect to a particular website named in the code. The URL named was http://www.iuqerfsodp9ifjaposdfjhgosurijfaewrwergwea.com/
Out of curiosity he checked the domain and found that it remained unregistered. He registered the same and it acted as a “Kill Switch” for the malware.
The person has admitted that when he registered the domain he was not aware that it would act like a kill switch but since the domain looked strange, he tested if it was available and went on to register it.
The kill switch doesn’t help devices WannaCry has already infected. But by registering the domain, and then directing the traffic to it into a server environment meant to capture and hold malicious traffic (“sinkhole”) some time has been bought for systems.
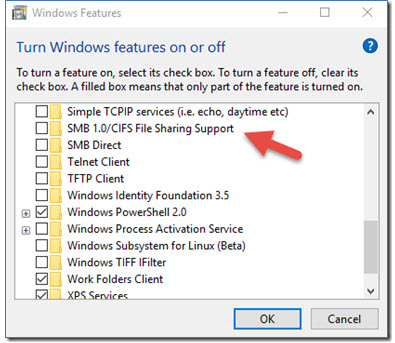 Additionally some security specialists advised disabling of the SMB 1 in windows features which comes activated by default. In fact even as back as an year, a security specialist categorically stated (Refer here) that this “Server Block Messaging Protocol” had outlived its utility and has no place in the modern world of malicious hackers. It can be easily disabled by going into “Turn off/on windows features” and unchecking the feature.
Additionally some security specialists advised disabling of the SMB 1 in windows features which comes activated by default. In fact even as back as an year, a security specialist categorically stated (Refer here) that this “Server Block Messaging Protocol” had outlived its utility and has no place in the modern world of malicious hackers. It can be easily disabled by going into “Turn off/on windows features” and unchecking the feature.
I am not sure if CERT-In had observed this opinion and converted it into an “Advisory”. It is this sort of advisory that would be useful to the people.
In the meantime, the ego of the hackers who introduced the WannaCry version 1 with a kill switch which was decyphered quickly has been hurt and we already have a notice that a new version of the malware has been released without the kill switch.
In view of this, the need to implement the security measures including applying the patch provided by Microsoft and disabling SMB1.0 becomes critical. Additionally, avoiding clicking on phishing mails and attachments also become necessary to be reiterated.
Some of the protective measures that people may try are as follows:
(Kindly beware that there would be phishing and fake sites offering such solutions which may themselves infect your company. Check if you are on a genuine site before proceeding further.)
- CERT Advisory from Cyber Swachcha kendra
- Kasparesky System Watcher: (Works on Endpoint Security)
- Guide at PCRISK.com
- Malware Bytes
- Bitdefender solution
- Sophos Solution
- TrendMicro solution
The best solution for “Ransomware” however remains to keep an off network data backup and complete segregation of critical systems from e-mail and internet threats. Ensure that the backup is accessed and operated in a secure environment so that the backups would not be infected during the process of updation or retrieval.
Naavi
Related Articles