With the increased use of Cloud as an infrastructure for data storage and processing, some aspects of the Cloud functioning pose serious challenges to the data protection compliance which needs a debate by experts.
The essential aspect of data protection laws is to provide a choice to the data subject to be able to access the personal data and if required ask for updation, portability and erasure.
The Data Protection Officer (DPO) is responsible for the compliance of aspects under the law and has to exercise control on how the personal data of data subjects can be discovered in the pool of corporate data that is scattered across the cloud (often multiple clouds), ensure that Consents are tagged to each such data set, and whenever any correction is to be made, it is synched at all the location centers.
Further, if the personal data and the associated profile needs to be ported or erased, the DPO should be able to ensure that the personal data associated with a given data subject is gathered without any omission and ported. If the information has to be erased, the DPO should be able to confirm that the personal data set of the given individual has been erased from all locations except those locations where it is required to be maintained by virtue of the company’s legitimate interests or because of law enforcement or national security reasons.
The task of personal data identification, consent tagging, porting and erasure is a difficult task even if the entire data is handled through the company’s own data center since there is always a tendency for personal data to get scattered in the resources of the company particularly in an unstructured format.
In the extraordinary situation that we are presently in where most companies had to introduce Work From Home under the COVID 19 lock down conditions, the corporate data access had to be given to employees from their home devices without proper preparation as to the security requirements. This could have spread the sensitive personal data of the data subjects to many of the employees personal devices.
In such a situation, all the designated rights of the data subjects/principals are all subject to “Emergent Exceptions”.
Whenever a suspected data breach incident is reported, the first task of the DPO is to confirm the breach through an investigation and then an attempt to preserve the evidence through forensic measures. This is not only required to meet the demands of the Data Protection Authority subsequently, but is also a legal obligation under Cyber Crime laws.
If the DPO fails to meet the requirements, he would not only make the company liable for higher levels of fines for lack of proper post-incident response and also for criminal prosecution of the company’s CEO, Directors or CISO, besides himself.
When a company is maintaining its own data center to which it has physical access, several forensic methods may be available for the compliance. Some of these such as “Discovery of Personal Data”, “Consent Tagging” etc may be possible even in the cloud environment. But when it comes to portability and erasure, the cloud infrastructure presents a tough situation where the DPO is completely dependent on the Cloud Service Provider (CSP). If the client is a small entity and the CSP is an Amazon or Microsoft, it is clear that the DPO has no freedom to get what he may want from the CSP and he would be entirely at the mercy of the CSP to meet the compliance requirement of the cloud user.
Some of the Data Protection Contracts of Data Controllers which were developed in the pre-GDPR era had taken into consideration data storage in the company’s own data center and had Incorporated clauses which were feasible for implementation in that scenario. However with the migration of storage and certain functions to the Cloud, many of the data processors continue to function under the legacy contracts which contain provisions which are impossible to fulfill in a cloud scenario.
In many occasions, the clients from US and even EU may use their old contract format and not revise it to meet the changed circumstances of both the new responsibilities under GDPR and the use of cloud for storage as well as processing. The Indian processors may find it difficult to convince their clients that the contractual clauses are ab-initio not applicable to the system of data processing that both might have otherwise agreed to. Identification of such situations is essential for Indian data processors to protect themselves from agreeing to do what they know they cannot do.
One such condition we often find in these contracts is the “Data Erasure Standards” to be used both when the personal data has to be first mounted on a new hard disk and also when it has to be deleted permanently. The Data Erasure standards such as DOD 5220.22 M or Bruce Schneier’s algorithm or any other method is developed for hard disk forensics and can apply where the entire storage system is under the control of the data controller/processor/fiduciary. But they donot apply when the data is stored in the cloud where the facilities are shared with others.
Also the techniques of “Deleted Data Recovery” that can be used in Disk Forensics does not function in the shared data storage facilities where the user has only control over certain number of bytes of storage space spread over a non contiguous space within the hard disk.
Further most storage systems even within a computer have migrated from hard disks to SSDs, and the file systems work differently making it difficult to use legacy forensic systems to carry out forensic investigations.
While some of the challenges mentioned above is not within the control of the DPO to rectify, it is necessary to recognize these limitations and factor it into the data processing agreements as “Disclaimers”.
I look forward to receiving a feedback for Forensic experts to identify the “Limitations of traditional forensic techniques in a cloud environment” and finding solutions to Data Protection Regulatory compliance.
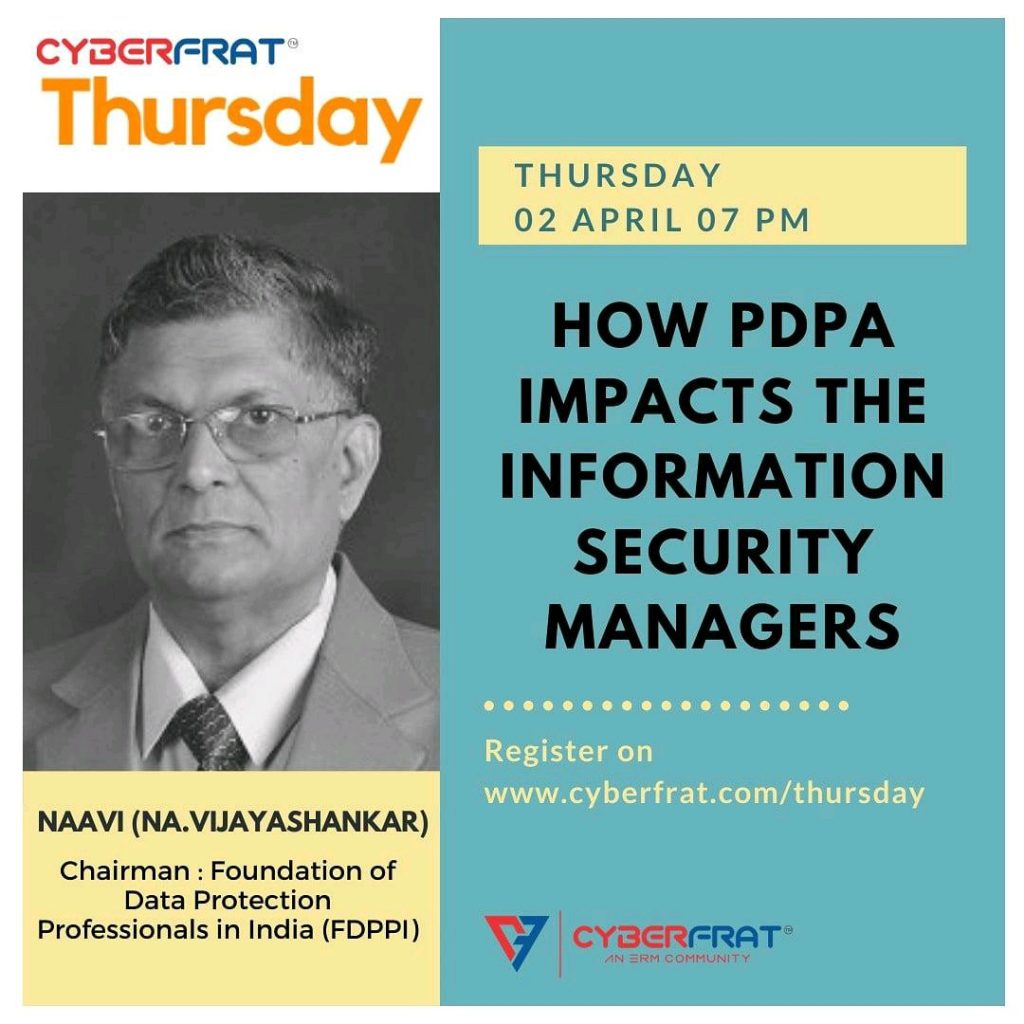
Naavi
Reference:
Data Sanitization for cloud storage