The way the underworld for Cyber Crime tools has developed indicates how complicated is the world of Cyber Crimes from the law enforcement issue. Cyber Criminals are difficult to catch both because they are anonymous and spread across the globe and also because they are technically a step or two ahead of the best of the law enforcement. Also the Cyber Criminal has lot of time at his disposal to plan and commit a crime while law enforcement has only a limited time before the evidences start fading. Additionally the law enforcement has to deal with issues of Privacy and Freedom of Expression while the criminal is not bound by any norm or ethics.
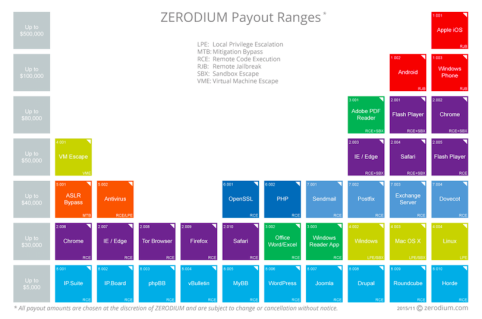
One manifestation of this asymmetric warfare is the announcement of an open price list for Cyber Crimeware by a firm which is considered as a “Broker” for buying and selling Cyber Crimeware. A company called Zerodium has put up a price list for different categories of exploits that people can buy. At the same time if there are any sellers, they can also use the chart for valuing their exploits.
The following is the chart published in an article at wired.com that indicates the current price of crimeware.
The pricelist indicates prices of upto $500,000 (Rs 3 crores) as annual subscription. It is unfortunate that the global law enforcement agencies have admitted their inability to control Cyber Crime or the illegal trading of such Crimeware by themselves subscribing to such services.
Zerodium proclaims itself to be a firm that pays premium rewards to security researchers to acquire and previously unreported zero day exploits affecting widely use operating systems, software and/ devices. Zerodium claims that normal Bug Bounty programs pay a smaller reward while it pays high rewards and focusses on high-risk vulnerabilities.
What is disturbing however is that Zerodium may also sell these by subscription. Though the company claims that it would not sell the exploits to oppressive Governments, the very fact that it is in the business of selling crimeware indicates that it is primarily prepared to sell for money.
It is possible that in due course ISIS may be able to infiltrate this organization or even force it to part with exclusive exploits that can be used against humanity. It is interesting to note that Zerodium is funded by a French firm Vupen and if for some reason the exploits fall into the wrong hands, then it would be ironical that a French firm itself would be responsible for the growth of ISIS.
While the concept of providing an appropriate reward for researchers is fine and I have also advocated it in the recent past (See: Bug Bounty Program from Government is required) ,my recommendation is that it has to be maintained by the Government agencies. (The fact that agencies like NSA have used it as Cyber war weapon is known and needs to be prevented separately by the checks and balances built in the system).
At the international level, a consortium of few countries need to manage such a program so that the exploits donot fall into wrong hands.
I suggest Prime Minister Mr Narendra Modi to start a discussion with global leaders and just has he has mooted the idea for Solar Energy consortium and Counter Terror Consortium, he can promote the concept of “Cyber Defense Consortium” which can operate this buying of exploits as a Bug Bounty program. The exploits however should be neutralized by quick patching so that they should never be available as a Zero day exploit.
Naavi
Related Article in infosecurity-magazine