On October 27, 2009, Government had issued a notification under Section 69 of ITA 2000 titled Information Technology (Procedure and Safeguards for Interception, Monitoring and Decryption of Information) Rules, 2009.
This rule had a clause 23 which stated as under:
Destruction of records of interception or monitoring or decryption of information.—
(1) Every record, including electronic records pertaining to such directions for interception or monitoring or decryption of information and of intercepted or monitored or decrypted information shall be destroyed by the security agency in every six months except in a case where such information is required, or likely to be required for functional requirements.
(2) Save as otherwise required for the purpose of any ongoing investigation, criminal complain or legal proceedings, the intermediary or person in-charge of computer resources shall destroy records pertaining to directions for interception of information within a period of two months of discontinuance of the interception or monitoring or decryption of such information and in doing so they shall maintain extreme secrecy.
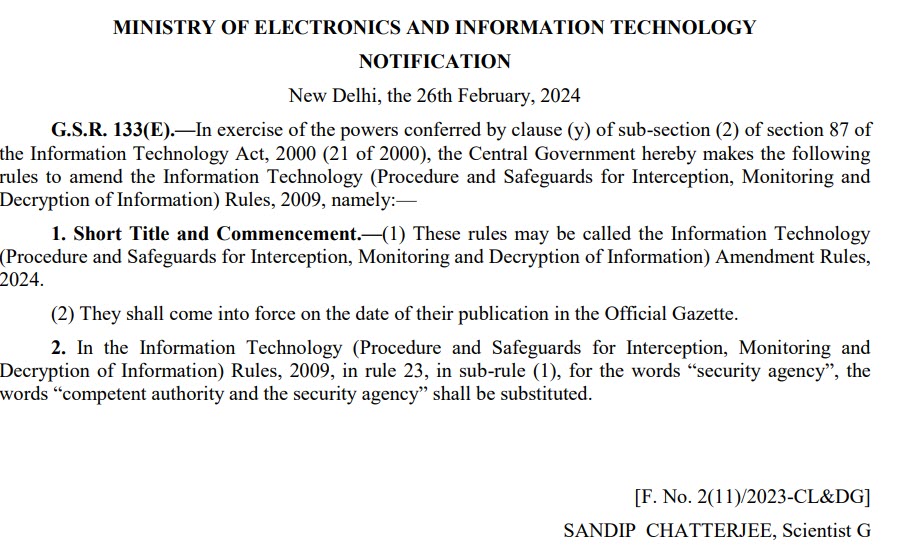
Now the current gazette notification states as under:
The Indian express commented that the rules have been amended to broaden the powers of the centre to issue directions to destroy digital evidence and to allow the home secretary or other bureaucrats to issue directions to destroy digital records.
On a proper reading of the rule it appears that the insinuations of the Indian Express (which no doubt will soon be echoed by the Anti Government media) is wrong. The rule suggests that the power to remove the information collected during an investigation process shall not be exercised by the security agency but by the authority which actually gave the permission or had the power to give permission for the monitoring. This is logical and appears to correct the possibility of misuse of the authority by the security agencies.
Under the rules, powers had been given exclusively to a “Competent Authority” to carry out the interception or monitoring or decryption of information. Any agency other than the “Competent Authority” indulging in such activity would become an “Unauthorized access” under Section 66.
To take care of unavoidable circumstances, it was provided that such orders may be issued by an officer not below the rank of a joint secretary duly authorized by the competent authority.
It was also provided that in case of emergencies and in remote areas where the obtaining of the permission from the “Competent Authority” or the “Designated Officer” was not feasible, the interception etc may be carried out with the prior approval of the Head or the second senior most officer of the security and law enforcement agency (hereinafter referred to as the said security agency) at the Central level and the officer authorised in this behalf, not below the rank of the inspector General of Police or an officer of equivalent rank, at the State or Union territory level;
In all cases where the delegated authority was exercised, such enforcing agency (Designated officer or the police officers etc) were required to inform in writing to the competent authority about the emergency and the action taken within 3 working days and obtain approval. If the approval was not available for 7 working days, the action of monitoring etc was expected to be terminated.
What the recent amendment states is that where such monitoring has commenced and certain data has been collected, the destruction of such data shall be done only with the instructions of the competent authority and not the security agency.
In other words, the security agency which is given the emergency powers to collect data is not permitted to play with it and destroy it when permission is denied by the competent authority.
This is therefore for “Preserving digital evidence” and not “Destroying digital evidence” as the news paper reports.
It is unfortunate that certain reporters of the media and the media themselves are ignorant and look at any action of the Government with coloured ideas. They must admit their ignorance and provide clarification. Otherwise this will be a “Fake News”.
I will not be surprised if this issue is taken to Court and some ignorant Judge perhaps in a High Court passes an order to stay the notification. A similar incident happened when Mumbai High Court gave a split verdict in the case of “Setting up of “Fake News Alert” by the Government to protect fake news about the Government being spread by the vested interests. The Court failed to understand the implications of the proposed amendments and the limited role of PIB in the context and declared that it was a freedom of press issue. In the past, in the celebrated Shreya Singhal Judgement Supreme Court itself displayed ignorance and gave a faulty judgement considering “Publication” as equivalent to “Messaging”.
I hope the news reporters understand such issues before they report.
One possibility is that State police in some occasions might have collected some investigating details using the powers under Section 69 of ITA 2000 and may like to destroy it before the NIA takes over the investigations. Such issues are now common in many states where there are opposition Governments. This amendment prevents the State level agencies exercising the powers as an emergency and later destroy the data if it is inconvenient to them. The amendment therefore has to be welcome as tightening up of the rules.
Naavi








