The system of Section 65B (IEA) Certification was born along with Information Technology Act 2000 and has been in place with effect from 17th October 2000. However, it was only in 2015, after the P.K.Basheer judgement of the Supreme Court stating that Section 65B certificate is mandatory for all electronic documents, that there was a realization by the legal community. Now in many of the lower Courts, judges are asking for electronic documents to be certified under Section 65B.
As a result, there is now a scramble for finding out the format in which the certificate is required to be provided. Many are trying to find out a “Standard” format that can be used in all certificates.
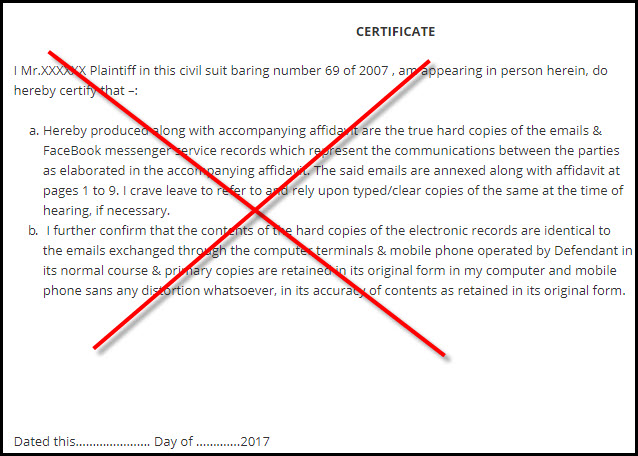
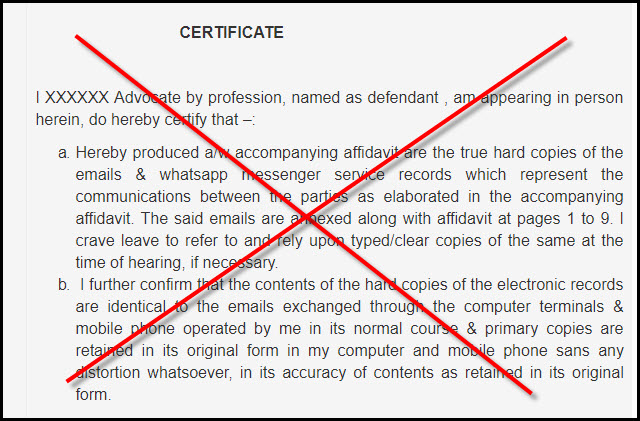
One such standard format which is being floated around is an “Affidavit” format since “Affidavit” is the most familiar document in our legal system.
Every body in the legal fraternity has respect for the document when it is called “Affidavit” and wants to file an affidavit as a ritual for any statement to be made to the Court. Courts also look at it as a procedural requirement rather than a committed declaration.
There are not many instances where a person giving a false affidavit is punished for perjury though every body knows that when the petitioner and the respondent both present affidavits swearing some thing exactly opposite, only one is swearing on a truthful statement and the other is making a false statement under oath.
Technically there could be a case where both the petitioner and the respondent may believe that their statement is true and are therefore not making the statements in bad faith. But such cases are few where some interpretation or inference is involved and not facts. Most are cases where on a matter of fact two diametrically opposing affidavits will be filed in a Court as if it is a matter of right to lie before the Court in self interest. Courts are also lenient in such cases and are not punishing people who deliberately file false affidavits to mislead the Court.
We must first agree that just because a statement is made under the title of an “Affidavit” and on a stamped paper, it does not acquire sanctity. What is stated there in and whether the person has the knowledge that the statement is true is important.
In the case of the Section 65B affidavits, the statement may only say that the document filed as a print out “identical to the electronic document” which is available in the computer or mobile. But this is not sufficient for the document to be accepted under Section 65B.
In our previous article “An Affidavit will not be a proper format for Section 65B Certificate”, we had indicated why the Affidavit format used by some is not the correct format. Many have since asked me to clarify why I think so, particularly when some courts have accepted the affidavits.
Without meaning any disrespect to any Court, I would like to say that from 17th October 2000 till date many Courts have been accepting electronic documents without any certificate, let alone in the correct format in which Section 65B certificate is required. This does not make such submissions as acceptable under law.
During all these years, CEAC has been producing certificates in the “CEAC Format” which according to our humble opinion was what is envisaged under Section 65B and Courts have accepted this without any problem.
However, if some body asks me to publish a “Standard” format which others can also use, it is not possible. I am not saying this because the format is a “Trade Secret” but because each certificate is unique and distinct to the type of document and the manner in which it was observed and recorded.
In this respect I consider that a Section 65B Certificate is like the “Digital Signature”.
A Digital Signature is a combination of a representation of the person signing an electronic document and the content of the electronic document. Hence if the person is different or the document is different, the digital signature file is different.
Similarly, a Section 65B Certificate is uniquely tied to the content of the electronic document which is the subject of certification and the process in which they were experienced by the person who is providing the certificate. Hence there is no single format fit for all cases.
In the first ever case (State of Tamil Nadu Vs Suhas Katti, AMM Court Egmore, Chennai) in which CEAC filed a certificate signed by Naavi, the subject document was in a server of Yahoo Inc and was accessible within a “Group”. The document was certified in support of the Prosecution and I was also examined as an “Expert Witness” and cross examined. What the Court thought of the process was also briefly reflected in the judgement (Copy available on www.ceac.in).
Immediately there after, the same Court invited me to observe a “CD seized from a crime scene” and certify the contents there in. I did it for the Court.
Subsequently, I have certified a variety of documents such as “Web Pages”, “Documents in a Corporate Network computer”, “Mails received or sent by a person visible in his/her email server”, SMS or WhatsApp messages on a mobile, Blackberry encrypted files saved on a computer, CCTV footage, Audio visual files etc.
As one can guess, each of these instances are unique and my observations run in some cases to hundreds of pages and the Certified copies submitted have even run to around 1700+ pages in one case.
Most of the times the electronic documents are on an “As is where is” basis. In some cases, the report may view further documents with a forensic tool which also is certified under Section 65B.
I suppose people will now appreciate why a Section 65B Certificate cannot be put on a standard format atleast when CEAC is involved with its own reputation to maintain.
I also make it clear that CEAC Certification like any Section 65B Certificate is for admissibility of the electronic document and subsequently Court may invite a Section 79A registered “Digital Evidence Examiner” (Government Agency registered for the purpose…none has been registered so far) and subject the electronic document to any further forensic examination.
In some cases, I am being asked if the Section 65B Certificate can be given by the plaintiff or the respondent himself or his lawyers. I have maintained that this will be considered “Self Serving” and reduce the value. Further the advocate giving a certificate may not be advisable since he becomes a witness to his own case.
A “Trusted Third party” is always preferred.
CEAC may be one such choice but need not be the only choice. If the trusted third party is credible, it would make the work of the Judge easier and he may avoid the need for every electronic document to be submitted to a Section 79A certified Government agency for verification.
If the certification agency is credible as per the Judge, there may also be no need to examine the Certifier as a witness also. Further, the Certificate given by the Certifier to the person at whose instance it is provided, may be submitted by him to the Court under his affidavit stating that this is the document submitted by the Certifier and this should be sufficient for the Court to admit the electronic document.
There could be some minor disagreements as to the procedure involved in submission which each Court may try to decide on its own but this would get standardized over a period of time.
While on the subject, I will also have to mention another issue that confronts CEAC from time to time which arises from the lack of understanding the Section 65B certification process and format.
Many times the users are unable to understand the effort required in extracting the electronic documents and provide the certificate and often are disappointed that even me known for free service most of the time quote a minimum of Rs 5000/- for the service. On the average the actual cost could be even higher and those who are accustomed to paying Rs 1000 for a lawyer to send a notice find it difficult to appreciate the value. Similarly, some ask for certification of a print out taken by them which I refuse. I have however done many “Remote Observation and Certification” where the user is not right in front of me but sitting say in USA.
In one recent case, a software professional engaged in a matrimonial dispute used the services for CEAC certified E Mail Delivery to the respondent which was critical to the case. But even he was unable to appreciate the value of the service. Many times, when we approach a company for a software and they quote a few lakhs of rupees, we wonder why a software should cost so much. Similarly those who donot understand the service are unable to also understand the value of the service and the cost involved.
It is only when the see that the CEAC certification under Section 65B is not a simple affidavit will they realize that the costs are not only reasonable but down right a steal.
I have elaborated this process for the reason that some of the persons asked me specifically to explain why the affidavit format is not favoured by me and I could sense that some of them may be having doubts as to whether I am rejecting a simple and cost effective requirement with some thing more complicated and expensive for personal vested interests.
I hope I have made things clear at least now.
Naavi