Information Assurance Framework
for Health Care Industry
(IAF4HC)
Part III-Modular
Approach to Information Assurance
Information Assurance (IA) is an augmented concept of
Information Security and extends the three core principles of IS
namely Confidentiality, Integrity and Availability (CIA), to
Authentication and Non Repudiation, and incorporates Legal
compliance as the second dimension.
For each of these aspects of information assurance, the
management need to ensure “Availability of the tools” and impose
necessary “Mandates”.
The “People Factor/Behavioural Science aspect” which is
referred to as the “Third Dimension of Information Security”
cuts across all dimensions of Information assurance such as
Confidentiality, Integrity, Availability, Authentication and Non
Repudiation.
At each of these levels the stake holders need to be made
“Aware”, their “Acceptance” need to be obtained and steps to be
taken to “Inspire” them into implementing the security
requirements.
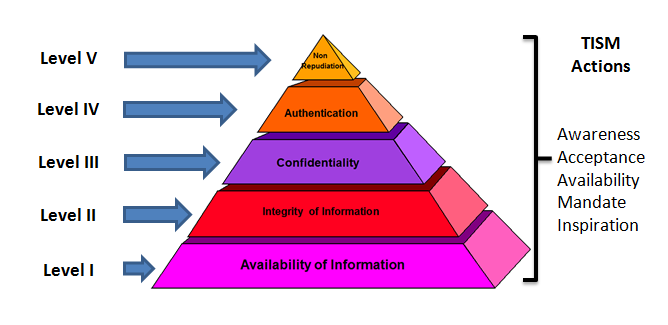
Under the Modular approach to Information Assurance, it is
suggested that we re-order the Information Security/Asssurance
objectives into different levels as follows.
|
Level |
Assurance Objective |
Actions |
|
I |
Availability
of required information to users |
Create Awareness*,
Obtain Acceptance*,
Make tools Available*,
Mandate* requirements and
Promote Inspiration* |
|
II |
Integrity
of information across time and space |
|
III |
Confidentiality
of information on a need to know basis |
|
IV |
Authentication
of information to fix ownership for all information
events |
|
V |
Non Repudiation
of action by any user |
(*
Refer Theory of Information Security Motivation)
It may be observed that the usual depiction of CIA
+Authentication and Non Repudiation has been put under a
hierarchy with priority of achievement moving from Level I to
Level V.
The above chart can also be presented in the more familiar
Pyramid form as follows:
The IAF4MI model ensures that most organizations which adopt
IT for business can achieve Level I. This level is basically
functional and most managements address this issue in the first
phase since this is directly responsible for the conduct of
business. DRP and BCP is part of this level at the simplest
form. At level II, the data integrity aspects need to be taken
into account At level III confidentiality aspects need to be
addressed. Level IV normally has a close relation to Level III
and has to be addressed more or less together. Level V addresses
the legal aspects of non-repudiation including evidence
management.
A further sub division of A, B and C can be made at each
level to distinguish between different levels of implementation
maturity such as “Implemented”, “Implemented and tested for
functionality”, “Implemented, certified as sustainable” etc.
A more detailed specification would be developed for each
level and to some extent will have to be customized for
different industries and different organizations.
The objective of the “Framework” is to provide a direction to
an organization to start implementing information security step
by step and reach an acceptable level over a period of time.
Each level will be a sort of a milestone to mark their journey.
For an auditor, the framework provides a guideline to measure
the compliance and provide its certification on whether the
organization has reached a given level of compliance.
Further refinement of the framework will be done in due course
based on the feedback received and the experience of Naavi and
Ujvala Consultants Pvt Ltd. I welcome the views and suggestions
from the public in this respect.
Naavi
November 18, 2012
[PS: Naavi's approach to IA is broader than the usually
recognized definition of IA. Hence Naavi has decided to use the
term "Total Information
Assurance" in place of Information Assurance in all his
discussions. As a result the acronyms will also be changed from
IA to TIA where ever applicable in all references in future...Naavi
...19th November 2012]


